You might have harvested many things upto now but what we are going to harvest today is something bad :)
Requirements:
- A Linux box (I'm using Kali Linux)
- theharvester program (already available in Kali Linux)
OK stop talking and start doing.
Fire up a terminal in your kali box and type this command:
theharvester -d hotmail.com -l 50 -b google
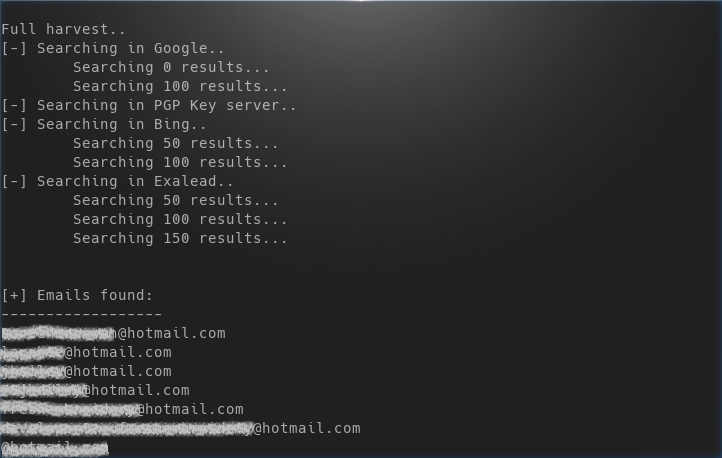
In a small amount of time you'll see your terminal flooded with 200 hotmail.com email address. What does this command mean?
theharvester is the tool name that we are using
-d <domain_name> specifies the domain (or website) who's email addresses we're looking for, in our case it was hotmail.com
-l <number> specifies the number of results that we want in the output, I limited it to 50
-b <source> specifies the source on which to look for email addresses, I specified google as the source
Besides google we can specify any of the follow as source:
google, googleCSE, bing, bingapi, pgp, linkedin, google-profiles, people123, jigsaw, twitter, googleplus, all
Here the last entry all means look in every available source.
Let's say you wanted to look in every available source they you should specify the following command:
theharvester -d hotmail.com -b all
-f is another great flag which can be utilized to save the output in case we want to SPAM them later (just kidding) or for other reasons (I'm thinking positive). -f flag saves the result in html or xml format. Let's do just that:
theharvester -d gmail.com -l 50 -b google -f emailaddresses.html
here -f flag is followed by the location where we want to store the file and the name of file, in our case we stored it in our pwd (present working directory) with the name emailaddresses.html.
Above picture shows an html output generated by harvester.
That's it for this tutorial hope to see you next time!
Related word
- Pentest Tools For Mac
- Hack Rom Tools
- Wifi Hacker Tools For Windows
- Hacker Tools Online
- How To Make Hacking Tools
- Hacker Tools 2020
- Tools For Hacker
- Hacker Tools 2019
- Pentest Tools For Android
- Kik Hack Tools
- Pentest Tools Apk
- Computer Hacker
- Pentest Tools Linux
- Pentest Tools Windows
- Hack Website Online Tool
- Hacking Tools Windows 10
- Hacking Tools Windows 10
- Hack Tools Pc
- Hack Tools For Ubuntu
- Usb Pentest Tools
- How To Hack
- Pentest Tools Framework
- Hack Tools Online
- Hacking Tools Mac
- Hacking Tools For Beginners
- Pentest Tools Free
- Pentest Tools Open Source
- What Are Hacking Tools
- Hackers Toolbox
- Hacking Tools Mac
- Pentest Tools Alternative
- Hacking Tools Online
- Pentest Automation Tools
- Hack Tools 2019
- Pentest Tools Website Vulnerability
- Pentest Tools For Android
- Hacker Tools Github
- Hack Tools For Mac
- Hacker Techniques Tools And Incident Handling
- Kik Hack Tools
- What Are Hacking Tools
- Ethical Hacker Tools
- Pentest Tools Free
- Hacker Tools Free
- Hack Tools Online
- Pentest Tools Bluekeep
- Pentest Tools Website Vulnerability
- Hack Tools Github
- Hacking Tools For Windows 7
- Hacker Tools Online
- Hack Apps
- Hack Tool Apk
- Pentest Tools Open Source
- Best Pentesting Tools 2018
- Pentest Recon Tools
- Nsa Hacker Tools
- Game Hacking
- Pentest Recon Tools
- Hack Tools Pc
- Hacker Hardware Tools
- Hacker Tools Linux
- Hacking Tools Github
- Hacker Tool Kit
- Hack And Tools
- Nsa Hacker Tools
- Pentest Tools Github
- Hacker Tools Apk
- Hack Tools For Mac
- World No 1 Hacker Software
- Hacker Tools 2019
- Pentest Tools Port Scanner
- Hacking Tools Pc
- Hacking Tools Hardware
- Hacker Tools Online
- Usb Pentest Tools
- Hacking Tools Usb
- Termux Hacking Tools 2019
- Hack Tools 2019
- Hack App
- Hacking Tools Online
- Hacking Tools Hardware
- Hacker Tools Apk
- Hacker Tools Free Download
- World No 1 Hacker Software
- Bluetooth Hacking Tools Kali
- Hacker Search Tools
- Pentest Tools Tcp Port Scanner
- Hackrf Tools
- Hacker Tools Software
- Hack Tools
- Pentest Tools For Ubuntu
- Hack Tool Apk
- Beginner Hacker Tools
- Hacker Tools List
- Hacking Tools Kit
- Hack Tools For Pc
- Best Hacking Tools 2019
- Ethical Hacker Tools
- Hacking Tools Kit
- Nsa Hack Tools Download
- Pentest Tools Github
- Pentest Tools For Mac
- Best Hacking Tools 2020
- Beginner Hacker Tools
- Hacker Tools Hardware
- Hacker Tools Hardware
- Pentest Tools Website
- Best Hacking Tools 2019
- Pentest Tools Tcp Port Scanner
- What Are Hacking Tools
- Underground Hacker Sites
- Hack Tools Download
- Easy Hack Tools
- Hacking Tools Windows
- Pentest Tools Free
- How To Install Pentest Tools In Ubuntu
- Wifi Hacker Tools For Windows
- Hacking Apps
- Hacking Tools Free Download




No comments:
Post a Comment